What Is DSPM? Data Security Posture Management Explained


Data security posture management (DSPM) is a cybersecurity discipline that continuously discovers sensitive data across cloud environments, assesses its exposure and access risks, and drives remediation to maintain a secure and compliant data posture. Unlike perimeter-based or infrastructure-focused security, DSPM centers protection on the data itself — identifying where it lives, who can access it, how it's being used, and whether the controls governing it are appropriate for its sensitivity.
First identified by Gartner in its 2022 Hype Cycle for Data Security, DSPM has become a foundational capability for enterprises managing data across Snowflake, Databricks, cloud storage, and multi-cloud analytics environments. But the original model has a problem: it wasn't designed for AI agents.
Traditional DSPM Wasn't Built for AI Agents. Here's What Modern Data Security Posture Management Looks Like.
The DSPM tools built between 2022 and 2024 solved a real problem: enterprises had lost track of where their sensitive data lived and who could access it. Scan, classify, report, remediate — that loop brought meaningful visibility to cloud data environments that had previously been opaque.
But that model assumed data was accessed primarily by human users, via known applications, on a relatively predictable schedule. In 2025, that assumption is broken.
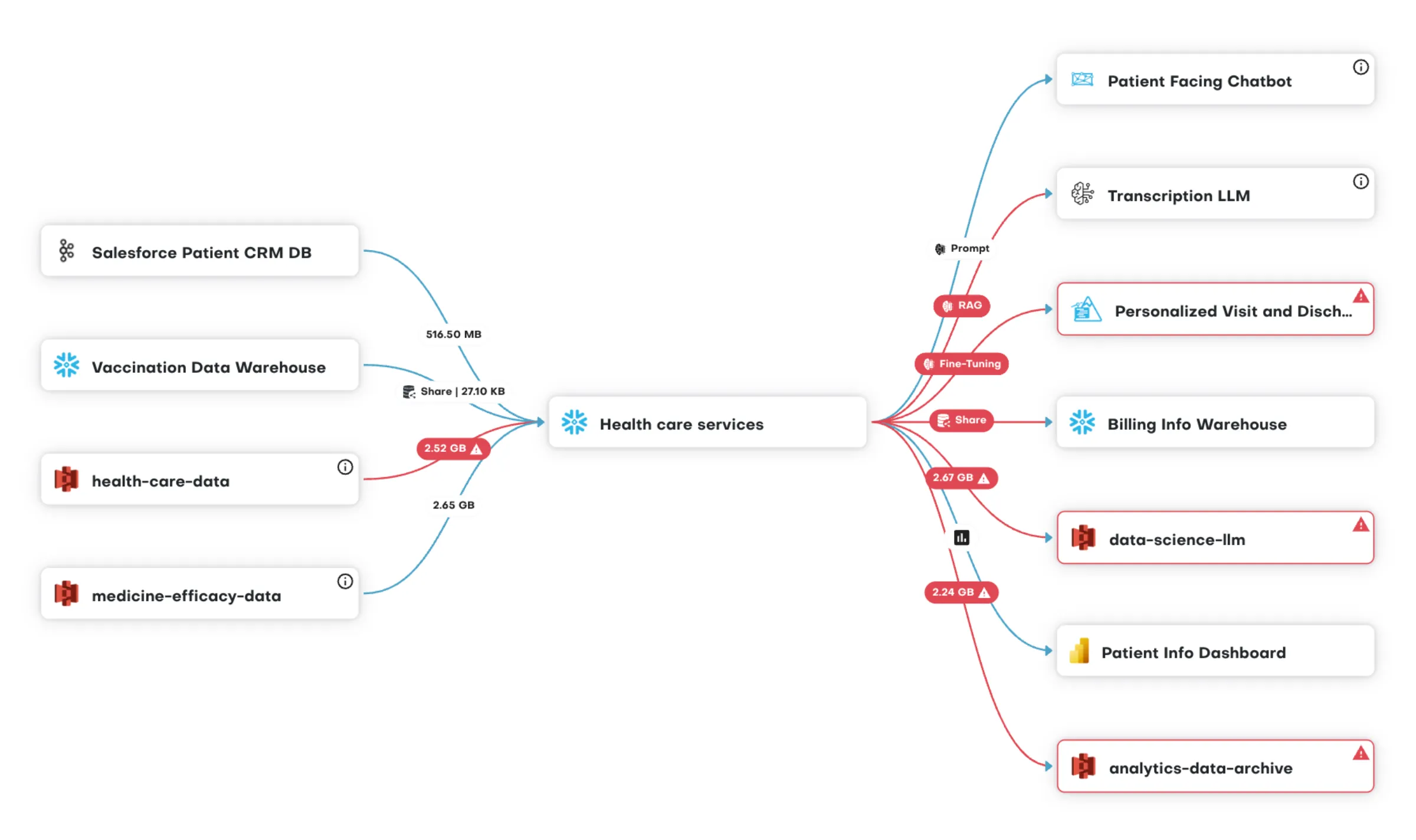
AI agents now query production data continuously — under service accounts with broad, persistent permissions that were set at deployment and never reviewed. LLM pipelines ingest sensitive data for training and inference. Automated workflows move data across platforms at a pace no human analyst can monitor manually. The non-human identities accessing enterprise data now outnumber the human ones in many organizations — and they're almost entirely invisible to traditional DSPM tools.
Modern DSPM needs to close two gaps the original model left open:
Posture without enforcement is just a better report. Identifying that a Snowflake schema is over-permissioned is valuable. But if the output is a finding that a security analyst has to manually translate into a policy change — through a ticketing system, coordinated with platform admins, applied one table at a time — the remediation lag creates its own exposure window. Modern DSPM connects posture insights directly to access policy enforcement, automatically.
Coverage must extend to non-human identities. AI agents, pipelines, and service accounts need the same entitlement governance as human users — with access scoped to the minimum necessary for each specific task, enforced at the data source, and auditable on demand.
The question isn't whether your data is classified. It's whether the right controls are in place at the speed AI moves — and whether your DSPM tool can enforce them, not just report on them.
How DSPM Works: Core Capabilities
Data discovery. DSPM continuously scans cloud environments — data warehouses, data lakes, object storage, analytics platforms — to maintain a live inventory of where data exists. This includes shadow data: datasets created by pipelines or copied for testing that exist outside official governance processes and are often accessible to far more users than intended.
Data classification. Discovered data is classified by sensitivity — PII, PHI, PCI, financial records, confidential business data — using automated scanning that identifies sensitive content at the column, table, and schema level. Classification is continuous, not point-in-time, so new data created by pipelines or AI systems is assessed as it appears.
Access risk assessment. DSPM maps who has access to sensitive data against what access is actually needed based on real usage patterns and business context. This surfaces over-permissioned users and roles, unused entitlements, and accounts with excessive privileges — the conditions that create the largest exposure surface.
Risk prioritization and recommendations. Rather than surfacing every potential issue simultaneously, DSPM prioritizes risks by severity and data sensitivity and provides actionable recommendations — right-sizing access, applying masking policies, revoking stale entitlements, or flagging data stores that lack appropriate controls.
Compliance reporting. DSPM generates audit-ready evidence by continuously validating data handling practices against regulatory frameworks including GDPR, HIPAA, CCPA, SOX, and PCI DSS — replacing manual audit preparation with automated, real-time reporting.
Continuous monitoring. DSPM monitors data access behavior over time, detecting anomalies — unusual query volumes, access outside normal patterns, data movement that suggests exfiltration risk — and alerting security teams to investigate.
DSPM vs. CSPM: What's the Difference?
Cloud security posture management (CSPM) focuses on the security configuration of cloud infrastructure — detecting misconfigurations in IaaS and PaaS environments and ensuring cloud infrastructure is hardened against attack. CSPM secures the environment that houses data.
DSPM focuses on the data itself. It operates at the layer of actual data assets — tables, schemas, files, columns — rather than the infrastructure around them. A misconfigured S3 bucket is a CSPM finding. A Snowflake table containing customer records accessible to 200 users when only 12 should have access is a DSPM finding.
The two are complementary, not competing. But for analytics-heavy environments where the highest concentration of sensitive data lives in Snowflake, Databricks, and Power BI, DSPM is the more critical capability.
DSPM for Analytics Platforms: Snowflake, Databricks, and Power BI
General-purpose DSPM tools typically focus on cloud storage. But for enterprises running analytics workloads, the most sensitive data — and the highest access risk — sits in Snowflake, Databricks, and downstream BI tools. Each presents specific DSPM challenges.
Snowflake. Data is created continuously through pipelines, shares, and Cortex AI queries. Access policies applied at the schema level may not reflect the sensitivity of individual columns. External shares and Cortex AI agents require the same governance as internal user access — and most DSPM tools don't reach that far.
Databricks. Unity Catalog governs access within the Databricks runtime, but that governance doesn't extend to data accessed outside the environment — through Power BI, direct S3 access, or AI agents. Data lineage across Databricks workflows is complex, making it difficult to understand where sensitive data flows without platform-specific coverage.
Power BI. Power BI is a downstream consumer of data governed in Snowflake and Databricks — but users accessing a report may be able to see data they wouldn't be permitted to query directly. BI-layer access needs to be consistent with upstream platform permissions, which requires DSPM coverage that spans both layers.
DSPM for AI: What It Means in Practice
As organizations deploy AI agents and LLM-powered analytics, three requirements have become critical:
Visibility into AI data access. Which datasets are AI agents querying? Which training pipelines are accessing sensitive data? DSPM needs to answer these questions for AI systems just as it does for human users.
Entitlement enforcement for non-human identities. AI agents and pipelines should access only the data needed for their specific function — scoped to the sensitivity of the requesting context, not the broad permissions of the service account they operate under.
Training and inference data protection. Sensitive data used in AI model training or surfaced in AI-generated responses requires the same classification and access governance as any other sensitive data — with the additional complexity that AI systems can aggregate, infer, and expose sensitive information in ways that direct data access cannot.
Organizations deploying AI without DSPM coverage for these scenarios are operating with a significant and growing blind spot.
How to Evaluate DSPM Vendors and Tools
The DSPM market has grown quickly, with vendors ranging from pure-play data security specialists to cloud platforms that have added DSPM capabilities. Five criteria separate strong implementations from tools that look comprehensive on paper:
A common trap in vendor evaluations: tools that demo well on cloud storage may have limited or proxy-dependent coverage for Snowflake and Databricks — the platforms where enterprise analytics data actually lives. Ask specifically about native integration depth for your primary data platforms before committing.
What Good DSPM Looks Like in Practice
TrustLogix customers have seen:
- Data access provisioning reduced from weeks to minutes
- 90% faster remediation of access misconfigurations
- 25% faster audit preparation vs. manual processes
- 60% reduction in operational costs through automated analysis
How TrustLogix Delivers Modern DSPM
TrustDSPM provides continuous data discovery, classification, and risk assessment natively across Snowflake, Databricks, Power BI, and AWS — operating on metadata without ever touching the underlying data, with no proxies, no agents, and no performance impact.
What separates TrustLogix from standalone DSPM tools is the closed loop between posture and enforcement. TrustDSPM connects directly to TrustAccess, which enforces fine-grained, attribute-based, least privilege access policies natively at the data source — translating risk recommendations into active controls automatically. TrustAI extends the same posture management and enforcement to AI agents, LLM pipelines, and automated workflows.
Recognized as a Strong Performer in the Gartner Peer Insights Voice of the Customer for Data Security Posture Management, based entirely on verified customer feedback, TrustLogix secures access to over 50 exabytes of data across hundreds of thousands of users at Fortune 500 enterprises in financial services, healthcare, and telecommunications.
From Visibility to Velocity: The Shift to Active DSPM
Most legacy DSPM tools are "passive"—they act like a security camera that records a burglary but doesn’t lock the door. They provide a long list of "Shadow Data" and "Over-privileged Users" but leave the actual fixing to your already-overburdened data engineering teams.
TrustLogix provides Active DSPM. By integrating discovery with our TrustAccess enforcement engine, we close the loop between finding a risk and fixing it.
- Find: Automatically identify sensitive PII/PHI across Snowflake, Databricks, and SQL Server.
- Analyze: Use behavioral analytics to see who is actually using the data versus who just has "zombie" permissions.
- Fix: Apply fine-grained, row-level security policies natively in the data platform to remediate over-privileged access in minutes, not weeks.
The DSPM-to-AISPM Bridge: Securing the AI Data Frontier
In 2026, you cannot have a secure AI strategy without a robust data posture. As organizations move from experimental LLMs to production-grade Agentic AI, the data used in RAG (Retrieval-Augmented Generation) pipelines becomes a primary attack vector.
TrustLogix extends DSPM into the realm of AISPM. We ensure that your AI agents don't become a "backdoor" to your sensitive data:
- LLM Data Governance: Prevent sensitive training data from leaking into model responses.
- Agentic Identity Propagation: Ensure AI agents inherit the same fine-grained access controls as the human user they are representing.
- Vector Database Security: Apply the same rigorous posture management to your vector stores (like Pinecone or Milvus) as you do to your structured warehouses.
The Proxyless Advantage: DSPM Without the "Security Tax"
The biggest barrier to DSPM adoption is often the "performance tax"—the latency introduced when security tools force data through an invasive proxy or sidecar.
TrustLogix is built on a Proxyless Architecture. Unlike competitors (such as Immuta or Satori) that sit in the data path, TrustLogix operates as a cloud-native control plane.
- Zero Latency: Queries run at native speeds because the security logic is "pushed down" into the platform itself.
- Maximum Privacy: Because we are proxyless, TrustLogix never "touches" or sees your raw data. Your data stays in your environment, maintaining 100% data residency compliance.
- Simplified Architecture: No complex networking changes or certificate management are required to get full DSPM visibility.
Frequently Asked Questions
What is data security posture management (DSPM)?
Data security posture management (DSPM) is a cybersecurity discipline that continuously discovers sensitive data across cloud environments, assesses its exposure and access risks, and drives remediation to maintain a secure and compliant data posture. DSPM focuses protection on data itself — identifying where sensitive data lives, who can access it, and whether those access rights are appropriate given the data's sensitivity and regulatory classification.
What is the difference between DSPM and CSPM?
CSPM focuses on the configuration security of cloud infrastructure — detecting misconfigurations in IaaS and PaaS environments. DSPM focuses on the data itself — discovering where sensitive data lives, who has access to it, and whether that access is appropriate. CSPM secures the environment; DSPM secures the data within it. Both are necessary, but DSPM is the more critical capability for analytics-heavy environments.
What are the core capabilities of DSPM tools?
DSPM tools provide automated data discovery across cloud environments, continuous classification of sensitive data by type and sensitivity, access risk assessment that maps permissions against actual usage, risk prioritization and remediation recommendations, compliance reporting against frameworks like GDPR and HIPAA, and continuous monitoring for anomalous data access behavior.
Does DSPM cover AI agents and automated pipelines?
Traditional DSPM tools were designed for human user access patterns and typically don't cover AI agents, LLM pipelines, and automated service accounts. Modern DSPM for AI extends discovery, classification, and access risk assessment to non-human identities — ensuring AI systems access only the data they're entitled to see with the same governance rigor applied to human users.
How do I evaluate DSPM vendors?
Key criteria: native integration depth with your primary data platforms (Snowflake, Databricks, Power BI — not just cloud storage), whether findings automatically translate into enforcement or require manual remediation, coverage of AI agents and non-human identities, time to value, and whether policies can be expressed in business terms rather than just technical permissions. Ask vendors specifically how they handle non-human identity governance — it's where most tools still have significant gaps.
How does DSPM support regulatory compliance?
DSPM supports compliance with GDPR, HIPAA, CCPA, SOX, and PCI DSS by continuously validating data handling practices against each framework and generating audit-ready evidence — replacing manual audit preparation with automated, real-time reporting.
What does DSPM mean for Snowflake and Databricks?
In Snowflake and Databricks, DSPM provides continuous visibility into sensitive data across schemas, tables, and columns — including data created by pipelines, AI queries, and external shares. It surfaces over-permissioned roles, unused entitlements, and unprotected sensitive columns, and connects those findings to enforcement so that policy changes are applied natively within each platform without manual intervention.
How long does DSPM implementation take?
Cloud-native DSPM platforms with native integrations to major data platforms can activate in hours rather than weeks, with no agents or proxies to deploy.
Stay in the Know
Subscribe to Our Blog






