Why Many AI Companies Can't Solve Your Agentic AI Security Problem. But TrustLogix Can.


A Fortune 500 technology executive spent three days at one of the largest industry conferences of the year searching for a solution to his AI problem. Dozens of vendor meetings. He walked away from most of them frustrated. Not because the vendors lacked capability, but because they couldn't engage with the actual complexity of his environment. They had an answer. It just wasn't built for his reality.
Almost every one of them claimed they had the same capability. Same pitch deck cadence. Same security claims. Same proof points.
He couldn't tell them apart, and more importantly, none of them could tell him what would actually happen if their product ran inside his environment.
That sameness is not an accident. It's a symptom.
They Were Never Built for Your Environment
Here's the uncomfortable truth that many AI vendors are structurally unable to tell you: the hardest part of agentic AI security is not the AI. It's the data underneath it. And many of the companies flooding your inbox right now were built by people who have spent their careers above the data layer, not inside it.
They understand model behavior, agent orchestration, and prompt security.
But they do not understand what happens when an agent with excessive privilege reaches a decade-old Oracle instance sitting on-prem next to a Snowflake deployment that was stood up six months ago.
They haven't lived in that environment. Their architecture wasn't designed for it. And when you ask them the question directly, you will find that out quickly.
The Questions That Expose the Gaps
This is where the vendor selection conversation usually goes sideways. Executives hear a confident answer and interpret it as a complete answer. These are not the same thing.
Ask them the questions that expose the gaps.
Ask how they handle your on-prem infrastructure, not abstractly, but specifically.
Ask what happens to masking policies when multiple agents sit in line between a user and a cloud data source.
Ask whether they can enforce consistent policy across Oracle on-prem and Snowflake simultaneously, in real time, without requiring you to redesign your legacy architecture first.
The answers will tell you whether a vendor was built for your actual environment or for an unrealistic, cleaner version of it.
Your Reality: Hybrid, Legacy, and Moving Fast
The reason many AI security vendors can't engage with those questions is that they're solving a different problem. They're solving for the enterprise that already has a modern, rationalized data environment.
But that enterprise is a minority. The majority are running Databricks and/or Snowflake alongside Oracle and SQL Server, sitting on top of file servers and S3 buckets and on-prem infrastructure accumulated over decades. They have manual ticketing processes for access control. Built for humans and running at human speed.
Meanwhile, those same enterprises are under pressure to be AI-first. They have agents they built, agents they bought, and agents running right now that nobody fully sanctioned. And almost all of those agents are accessing data with more privilege than they should have, with no visibility of what they're actually doing at the end data source.
That's not an edge case. At enterprise scale, that's the norm today.
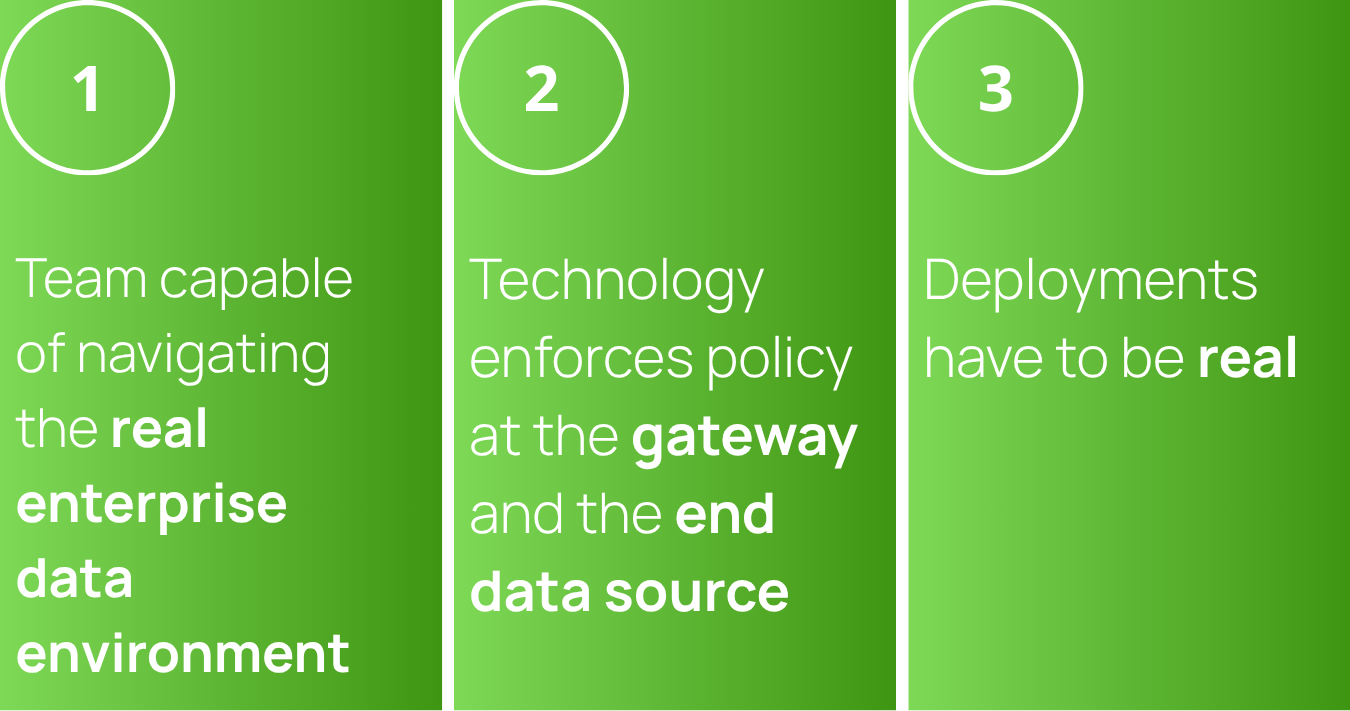
Three Things the Right Vendor Has to Get Right
The foundational requirement is a team capable of navigating the real enterprise data environment… a company built by people who have worked at the enterprise data layer long enough to recognize it on sight. Developers, solution architects, and founders who spent the time inside the data layer of enterprises like the ones you actually run. Not just observing from the application layer above it… and not just abstracting from the cloud around it. That means knowing what it looks like when an on-prem Oracle instance sits next to a Snowflake deployment, when file servers have been layered and patched for fifteen years, when three different agents are touching the same data source with permissions nobody fully reviewed. That depth of fluency is what keeps the hard architecture questions from ending the conversation.
The technology itself has to enforce policy at both the gateway and the end data source, across your full data ecosystem, regardless of where that data lives. One that resolves the human identity behind the agent, tracks agent-level privilege, and enforces fine-grained, attribute-based, purpose-based controls all the way down to the source, whether that data is in Databricks, Snowflake, Oracle, or a file server running on-prem. Not a log entry after the fact. Actual governance, at the source, in real time.
And the deployments have to be real. Not pilots in greenfield architectures, but production deployments inside heavily regulated companies running hybrid data infrastructure at scale.
What TrustLogix Was Built to Do
TrustLogix was built from that starting point. Our founders spent decades inside the data layer of real enterprise environments, and that background shapes every architectural decision we made. We are fully deployed in production at companies like AMD, BestEgg, Ericsson, and Jeffries. Almost all of those deployments span Oracle or SQL on-prem alongside either Databricks or Snowflake, and other cloud data sources, simultaneously, inside heavily regulated environments.
Those are the kinds of data ecosystems many AI vendors are simply unable to help you with.
The AI vendor landscape right now is extraordinarily noisy. It's difficult to tell one vendor's story from another. Many of those stories were written for a world that doesn't match yours.
Ask them to walk through your actual architecture. The on-prem Oracle instance, the hybrid file server, the three agents nobody fully sanctioned. See if the conversation changes.
The vendors who do not flinch at that conversation are the ones worth your time.
Stay in the Know
Subscribe to Our Blog






