Enterprise Data Access Control: The Complete Guide


Data access control is the combination of policies, technologies, and processes that determine who can access which data, under what conditions, and for how long. It governs every human user, service account, and AI agent that touches enterprise data across cloud platforms — and it has always been a foundational element of enterprise security.
The problem: the people, systems, and AI agents that need access to enterprise data are multiplying faster than the controls designed to manage them. In an era of multi-cloud architectures, AI-driven workflows, and escalating regulatory pressure, traditional approaches are buckling.
This guide covers what data access control means in a modern enterprise context, where the most common failure points are, what a mature approach looks like, and how organizations across healthcare, financial services, and telecommunications have transformed security from a bottleneck into a business accelerator.
What Is Data Access Control?
At its core, data access control answers four questions:
- Who is requesting access? (Identity — human user, service account, AI agent, or automated process)
- What data are they requesting? (Resource — tables, schemas, datasets, fields)
- Under what conditions is access appropriate? (Context — role, project, time, geography, data sensitivity)
- What should they be allowed to do with it? (Action — read, write, modify, share, delete)
These questions get answered through different access control models, each with different tradeoffs in flexibility and administrative overhead.
Access Control Models: RBAC, ABAC, and PBAC
Role-Based Access Control (RBAC) assigns permissions based on a user's job role. A data analyst gets read access to analytics tables; a DBA gets broader administrative rights. RBAC is intuitive and relatively easy to implement — but it doesn't scale well. As organizations grow, roles proliferate, overlap, and drift. The result is what practitioners call "spaghetti roles": a tangle of redundant, over-permissioned entitlements that's nearly impossible to audit or clean up.
Attribute-Based Access Control (ABAC) adds nuance by factoring in attributes — a user's department, location, clearance level, or the sensitivity classification of the data being requested. ABAC is more flexible than RBAC but can be complex to configure and maintain across large, changing environments.
Policy-Based Access Control (PBAC) goes further, combining identity, context, business rules, and real-time conditions into a single, dynamic policy framework. Instead of asking "What role does this user have?", PBAC asks "Does this specific request, by this specific identity, for this specific data, under these specific conditions, comply with enterprise policy?" PBAC is the most powerful model for enterprises managing complex, multi-platform data environments — and it's the foundation of modern data security platforms.
Why Traditional Data Access Control Breaks Down
For many enterprises, data access control started as a manageable problem. A few data warehouses, a defined set of users, manual approval workflows. Then the data ecosystem expanded. Cloud platforms multiplied. Teams grew. Contractors came and went. AI pipelines appeared. And the manual, role-based model that once worked became a liability.
Here are the most common failure modes:
1) Fragmented Controls Across Platforms
Modern data teams typically work across multiple platforms — Snowflake, Databricks, AWS, Azure, and more — each with its own native access control mechanisms. Without a unified layer above these platforms, security policies get duplicated, enforcement becomes inconsistent, and no one has a complete picture of who actually has access to what. A Fortune 500 healthcare company described the challenge bluntly: similar users across different business units ended up with vastly different access privileges, resulting in both over-provisioning and unnecessary restrictions — because there was no standardized policy framework spanning the entire environment.
2) Privilege Sprawl
Left unmanaged, permissions accumulate. A contractor finishes a project and their access is never revoked. A user changes roles and retains entitlements from their previous position. Service accounts for deprecated applications remain active. In one healthcare organization, 10% of contractor accounts retained access to sensitive data months after project completion — a finding that only surfaced through a formal access review. Without continuous visibility into what access exists versus what's actually being used, privilege sprawl is invisible until it becomes a breach or an audit finding.
3) Provisioning Bottlenecks
When access requests require manual review, cross-team coordination, and platform-by-platform configuration, provisioning takes days or weeks. Data teams waiting for access can't do their jobs. Projects stall. In regulated environments, the default response to uncertainty is often denial — which creates friction without improving security. One global telecom provider found that legitimate data requests were routinely blocked or delayed not because of genuine risk, but because approval processes were designed for a simpler era.
4) No Visibility, No Control
You can't protect what you can't see. Security teams without centralized visibility into data access activity can't answer basic questions: Who accessed this dataset last week? Which roles haven't been used in six months? Is sensitive data being shared externally? Without that visibility, security posture is reactive — organizations only discover access problems after audits, incidents, or regulatory inquiries.
"Our inability to centrally manage all of our data security policies across our data platforms hampered our ability to deliver value to the business in a timely manner. We needed a way to standardize and automate security control across all our tools, platforms, and clouds."— VP of Data & Analytics, Fortune 500 Financial Services Company
The Modern Enterprise Data Access Control Framework
A mature data access control approach in today's enterprise has several defining characteristics. It's unified across platforms, policy-driven rather than role-driven, and automated rather than manual. Here's what it looks like in practice:
Unified Cross-Platform Enforcement
Rather than managing access natively within each platform, a unified access control layer translates enterprise policies into platform-specific enforcement automatically. This means one set of policies governs access across Snowflake, Databricks, AWS, Azure, and beyond — with consistent application, centralized visibility, and a single source of truth for entitlements. Security teams stop chasing policies across disconnected systems.
Policy-Based Access Control at Scale
Dynamic, context-aware policies replace static role assignments. Access decisions incorporate the requesting identity, the data's sensitivity classification, the purpose of the request, organizational attributes (profit center, geographic assignment, project), and real-time risk context. This is what enables fine-grained access control without administrative overhead — policies do the work that would otherwise require manual review.
Least-Privilege Enforcement
The principle of least privilege — every user and system gets exactly the access they need, nothing more — sounds simple but requires continuous enforcement. In practice, this means automated detection of over-provisioned roles, unused entitlements, and excessive permissions, combined with the ability to revoke or adjust access dynamically as conditions change.
Non-Human Identity (NHI) Management
Service accounts, application IDs, bot IDs, API keys, and AI agents are now significant actors in enterprise data environments. They often receive the same access as — or more access than — the human users who deploy them, with less oversight and no natural lifecycle. Modern access control treats non-human identities with the same rigor as human users: scoped permissions, usage monitoring, and automatic revocation when no longer needed.
Real-Time Visibility and Audit Readiness
Continuous monitoring of who accessed what data, when, and why provides the foundation for both proactive risk management and audit response. Rather than reconstructing access history after an incident or inquiry, security teams have real-time dashboards and automated reporting that answer compliance questions on demand. DSPM is required for this.
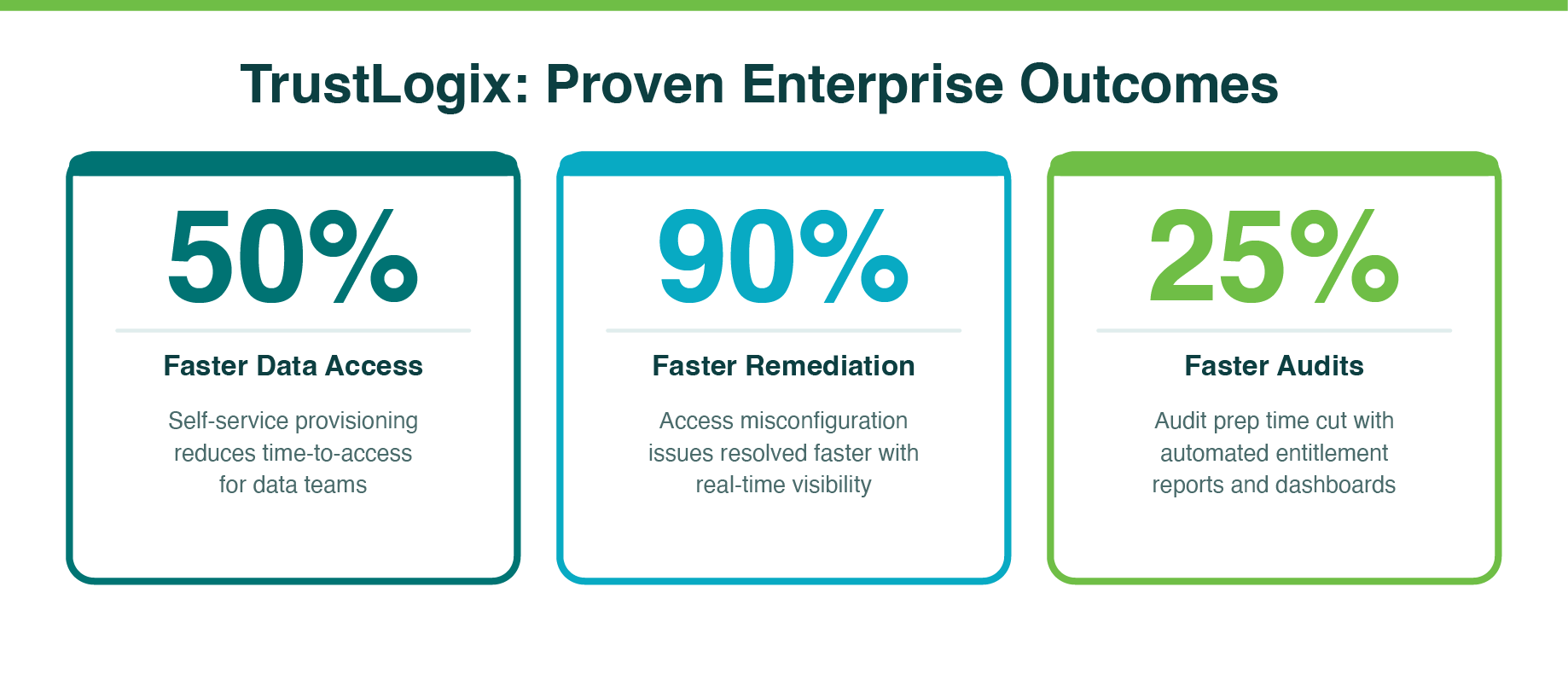
Organizations that have implemented unified, automated access control report 25% faster audit completion, 90% faster remediation of access misconfigurations, and provisioning timelines reduced from weeks to minutes.
Data Access Control for AI Workloads
AI agents, automated pipelines, and machine learning workflows have introduced a new class of data access risk — one that traditional access control frameworks were never designed to handle.
The core problem is speed and autonomy. Human users make deliberate, infrequent data requests that can be reviewed and approved. AI agents issue thousands of queries, chain data sources, act on behalf of users, and operate continuously — often with persistent credentials that were granted once and never revisited. Gartner has described this as the "velocity gap": humans can no longer govern data access at machine speed.
The specific risks this creates include:
- Over-permissioned AI agents holding standing credentials to entire datasets, far beyond what any specific task requires
- Opaque accountability — when sensitive data is accessed through an AI pipeline, it's often impossible to trace which agent, on whose behalf, accessed what
- PII and regulated data flowing into AI prompts and model training without appropriate masking or access controls
- Non-human identities — application IDs, service accounts, API keys — operating with privileges that outlast their intended use
The solution is dynamic, context-aware access controls that evaluate every data request against identity, purpose, and real-time risk — not a role assignment made weeks ago. Just-in-time access replaces standing privileges: entitlements are granted for a specific task and automatically revoked upon completion. Data masking ensures that sensitive fields are protected before they enter an AI context window or model training pipeline. And every interaction is logged with full auditability, mapping each request to the policy that governed it.
This is what it means to govern AI at machine speed — and it's where the next generation of data security platforms is focused.
Compliance and Regulatory Alignment
Data access control is not just a security function — it's the operational backbone of regulatory compliance. GDPR, HIPAA, SOX, PCI-DSS, and an expanding array of data residency laws all share a common requirement: organizations must demonstrate that sensitive data is only accessible to authorized individuals, that access is monitored, and that they can produce audit evidence on demand.
The specific compliance functions that automated access control enables include:
- Data residency enforcement: ensuring that regulated data stays within designated geographic boundaries and that employees in embargoed regions cannot access restricted systems
- Separation of duties: enforcing policy-level controls that prevent conflicts of interest across business units, roles, and functions
- Audit trail generation: providing immutable, timestamped records of every access event — who, what, when, and why — without manual compilation
- Third-party and contractor access management: tracking entitlements for external parties and ensuring access is revoked when engagements end
- Sensitive data classification integration: applying access controls based on the actual sensitivity of the data, not just the platform it lives on
Enterprises that have moved from manual to automated access control consistently report faster audits, fewer audit findings, and reduced exposure to regulatory penalties. The compliance benefit isn't just about avoiding violations — it's about shifting from reactive firefighting to continuous, demonstrable compliance posture.
What Good Looks Like: Real-World Outcomes
The proof of modern data access control isn't in architecture diagrams — it's in measurable business outcomes. Across industries, organizations that have implemented unified, automated access control have seen consistent results:
Healthcare
A Fortune 500 healthcare company operating Snowflake and Databricks across multi-cloud environments replaced a fragmented, manual RBAC model with a unified, policy-based approach. Provisioning time dropped from weeks to minutes through self-service workflows integrated with their existing ticketing system. Access misconfiguration remediation accelerated by 90%. Audit preparation time fell by 25%. And sensitive clinical, pharmaceutical, and financial data is now protected by granular policies that enforce least-privilege access across both platforms consistently.
"TrustLogix Data Security Platform proved instrumental in accelerating our data transformation journey. What distinguished TrustLogix was its capability to continuously monitor data access patterns and enforce least privilege principles across our environment."— Director of Data Governance and Operations, Global Healthcare Provider
Telecommunications
A global telecom provider managing 100+ data products across hybrid infrastructure deployed unified policy automation to replace siloed, manually enforced controls. The result: a 30% improvement in team productivity, data products delivered in half the time, and a security posture that shifted from reactive to continuous. Geography-based controls automatically enforce data residency compliance, and policy drift is detected in real time before it becomes a violation.
Financial Services
A Fortune 500 financial services company chose a proxyless, cloud-native architecture to simplify data security across their multi-cloud environment. Their CISO described the outcome directly: the platform provides strong, non-obtrusive data security controls consistently across all data platforms, managed from a single pane of glass — eliminating the constraints of native security controls and open-source tools while giving data owners appropriate control without requiring deep knowledge of underlying platform complexity.
How to Evaluate a Data Access Control Solution
If your organization is assessing data access control platforms, these are the capabilities that separate effective solutions from point tools:
- Cross-platform coverage: Does the platform enforce unified policies across all major cloud data platforms — Snowflake, Databricks, AWS, Azure — without requiring separate management in each?
- Policy flexibility: Can policies incorporate identity, organizational attributes, data classification, geography, and business rules? Can they adapt dynamically to changing conditions?
- Non-human identity support: Does the platform apply least-privilege principles and monitoring to service accounts, API keys, and AI agents — not just human users?
- Self-service provisioning: Can data owners approve and provision access without requiring IT intervention for every request?
- AI workload readiness: Does the platform support just-in-time access, dynamic masking, and full auditability for AI agent and automated pipeline activity?
- Audit and compliance reporting: Can the platform generate real-time entitlement reports, access activity logs, and compliance dashboards without manual data assembly?
- Architecture: Does the platform operate without proxies or agents that could create performance bottlenecks or single points of failure?
- Integration: Does it integrate with existing identity providers, ticketing systems, and SIEM tools?
The right platform eliminates the tradeoff between security and velocity. Access control should accelerate the work of data teams, not block it.
Conclusion: Security That Accelerates Innovation
The enterprises that are winning with data today aren't the ones with the most restrictive access controls — they're the ones with the most intelligent ones. Access control that's dynamic, unified, automated, and AI-ready doesn't slow data teams down. It gives them the confidence to move faster, knowing that security is enforced at the source.
The shift from manual, role-based access management to policy-driven, automated enforcement is one of the highest-ROI investments a data organization can make — not just for security and compliance, but for productivity, agility, and trust.
The question isn't whether your organization needs modern data access control. It's whether your current approach can keep up with the speed at which your data environment is evolving.
Frequently Asked Questions: Data Access Control
What is data access control and why does it matter?
Data access control is the set of policies, processes, and technologies that determine who can access which data, under what conditions, and for how long. It matters because uncontrolled access is one of the leading causes of data breaches, compliance violations, and audit failures. As enterprises scale across multi-cloud environments, maintaining consistent, enforceable access controls becomes both more complex and more critical.
What's the difference between RBAC, ABAC, and PBAC?
Role-Based Access Control (RBAC) assigns permissions based on a user's job role. It's straightforward to implement but becomes difficult to manage at scale — roles multiply, overlap, and quickly become inconsistent. Attribute-Based Access Control (ABAC) adds flexibility by incorporating attributes like department, location, or data classification. Policy-Based Access Control (PBAC) goes further, combining identity, context, business rules, and real-time conditions into a single dynamic policy framework. For enterprises managing complex data environments, PBAC delivers the precision and adaptability that RBAC alone cannot provide.
How do you manage data access control across multiple cloud platforms?
The core challenge is that platforms like Snowflake and Databricks each have their own native access control mechanisms, which leads to duplicated policies, inconsistent enforcement, and significant administrative overhead. The most effective approach is to implement a unified access control layer that sits above individual platforms — one that translates enterprise policies into platform-specific enforcement automatically. This eliminates the need to manage permissions separately in each environment and provides a single source of truth for who has access to what, across the entire data ecosystem.
What is least-privilege access and how do you enforce it at scale?
Least-privilege access means every user, application, or automated process receives only the minimum permissions required to do their job — nothing more. In practice, enforcing it at scale requires continuous visibility into what access actually exists versus what's being used, automated detection of over-provisioned roles, and the ability to revoke or adjust permissions dynamically. Without tooling to surface unused entitlements and eliminate redundant roles, organizations end up with privilege sprawl that creates both security risk and compliance exposure.
How does data access control support GDPR and HIPAA compliance?
Both GDPR and HIPAA require organizations to demonstrate that sensitive data is only accessible to authorized individuals, that access is monitored, and that they can produce audit evidence on demand. Automated access controls directly support this by enforcing data residency restrictions, limiting access to PII and PHI based on role and purpose, and generating real-time audit trails. Organizations that have moved from manual to automated access control have reported up to 25% faster audit completion and significantly reduced compliance exposure.
What are non-human identities (NHIs) and why do they matter for data access?
Non-human identities include application IDs, service accounts, bot IDs, API keys, and any automated process that accesses data without a human user behind it. They are one of the most overlooked access control risks — often over-provisioned, rarely reviewed, and difficult to track. As AI pipelines and automated workflows proliferate, NHIs now account for a growing share of all data access activity. Effective access control must treat NHIs with the same rigor as human users, applying least-privilege principles and real-time monitoring to all machine-driven access.
How is data access control different for AI workloads?
Traditional access control was designed for human users making deliberate, infrequent data requests. AI agents and automated pipelines operate at machine speed — issuing thousands of queries, chaining data sources, and acting on behalf of users without direct human oversight. This creates new risks: static API keys and standing privileges that persist far beyond their intended use, opaque accountability when sensitive data is accessed, and PII or regulated data propagating into AI prompts and models. Effective access control for AI requires dynamic, context-aware policies that evaluate every data request against identity, purpose, and real-time risk — not just a role assignment made weeks ago.
How long does it take to provision data access with a modern platform?
With manual processes, access provisioning typically takes days to weeks — requiring tickets, approvals, and manual configuration across multiple platforms. With an automated, policy-driven approach, that timeline compresses to minutes. Enterprises using TrustLogix have reduced provisioning time from weeks to minutes by integrating automated entitlement workflows with their existing ticketing systems, with data owners approving requests that are then provisioned automatically across Snowflake and Databricks simultaneously — delivering a 50% acceleration in data access without sacrificing security or audit integrity.
Ready to See It in Action?
TrustLogix helps enterprise data teams enforce unified, automated, policy-based access control across Snowflake, Databricks, and multi-cloud environments — for both human and non-human identities, including AI agents.
Schedule a complimentary demo to see how TrustLogix can reduce provisioning time, strengthen compliance posture, and give your data teams the access velocity they need.
Stay in the Know
Subscribe to Our Blog






